CS: Cryptography: Ciphers and Encryption
Practice with classic ciphers, keys, encryption, and security ideas
Practice with classic ciphers, keys, encryption, and security ideas
CS - Grade 9-12
- 1
Use a Caesar cipher with a shift of 3 to encrypt the message CAT. Shift each letter 3 places forward in the alphabet.
- 2
A message was encrypted with a Caesar cipher using a shift of 5. The ciphertext is MJQQT. Decrypt the message.
- 3
Using A = 0 through Z = 25, encrypt the letter R with a Caesar shift of 9. Show the modular arithmetic.
- 4
A substitution cipher maps plaintext letters to ciphertext letters using a secret shuffled alphabet. Explain one reason a simple substitution cipher is usually not secure against a determined attacker.
- 5
In English text, the letter E often appears more than any other letter. In a long ciphertext made with a simple substitution cipher, the symbol X appears most often. What might an attacker reasonably guess, and why?
- 6
Use the Vigenere cipher to encrypt the plaintext HI using the key NO. Use A = 0, B = 1, and so on. Add the plaintext value and key value modulo 26 for each letter.
- 7
Use the Vigenere cipher to decrypt the ciphertext UW using the key NO. Use A = 0, B = 1, and so on. Subtract the key value from the ciphertext value modulo 26.
- 8
A one-time pad can provide perfect secrecy when used correctly. List two conditions that must be true for a one-time pad to be secure.
- 9
Encrypt the 4-bit plaintext 1010 using XOR with the 4-bit key 1100. Show the result bit by bit.
- 10
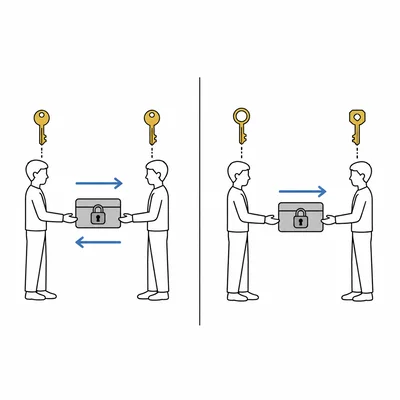
Explain the difference between symmetric encryption and asymmetric encryption. Include what kind of keys are used in each system.
- 11

A website uses HTTPS. Explain how encryption helps protect a user's password when it is sent from the browser to the website.
- 12
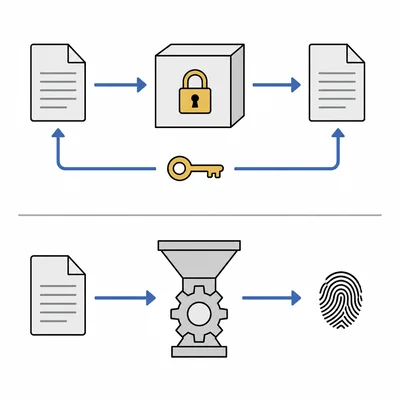
A classmate says, "Hashing is the same as encryption because both hide data." Explain why this statement is not correct.
Related Tools
Related Labs
Related Infographics
Related Cheat Sheets
More CS Worksheets
CS: Algorithms and Flowcharts
Grade 6-8 · 12 problems
CS: Arrays and Lists
Grade 9-12 · 12 problems
CS: Big-O Notation and Algorithm Efficiency
Grade 9-12 · 12 problems
CS: Binary Numbers and Number Systems
Grade 6-8 · 12 problems
More Grade 9-12 Worksheets
Linear Equations
Math · 8 problems
Cell Biology
Biology · 8 problems
Reading Comprehension
Language Arts · 8 problems
Historical Thinking & Evidence
Social Studies · 8 problems