Cybersecurity Fundamentals
Threats, encryption, and safe digital habits
Related Tools
Related Labs
Related Worksheets
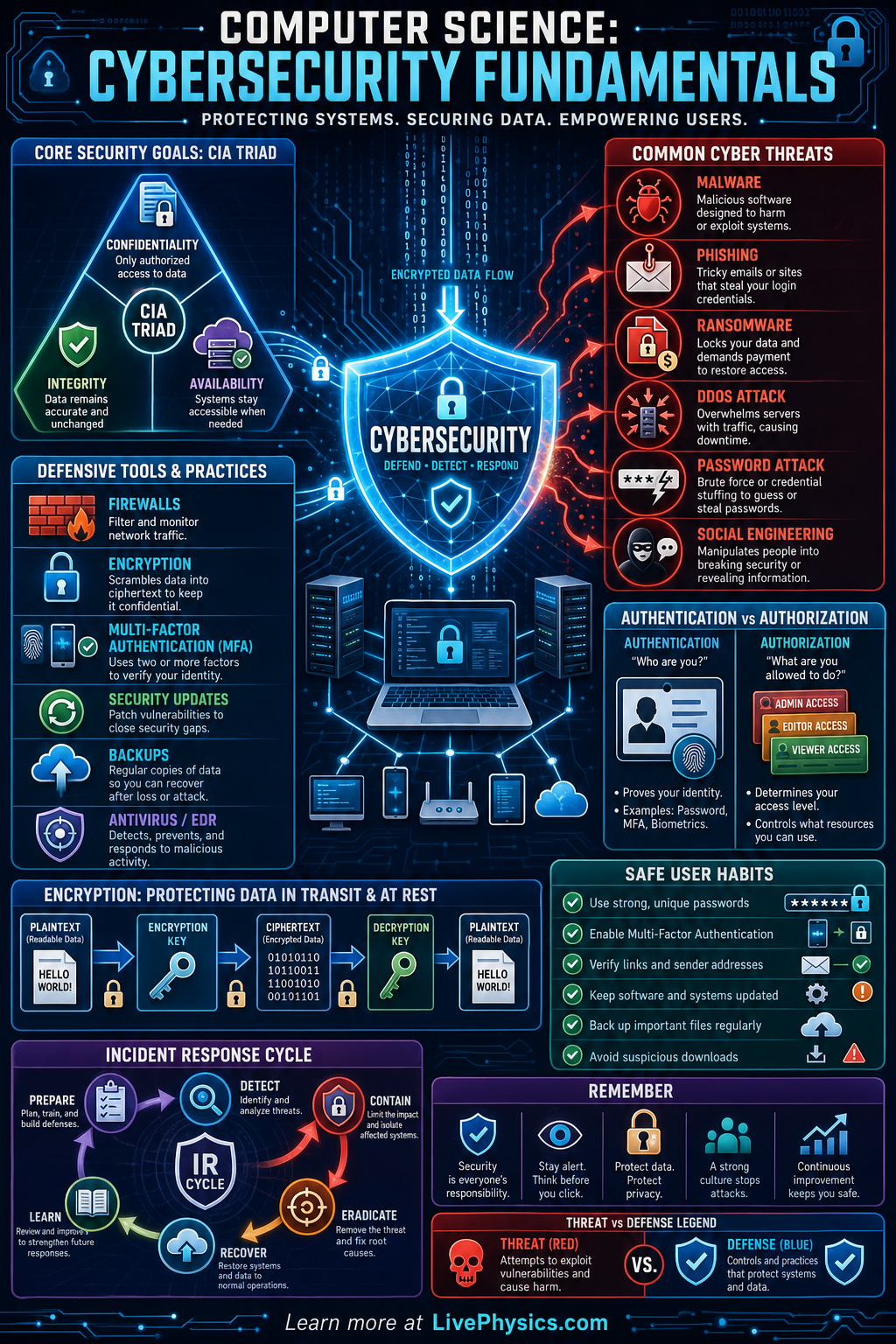
Cybersecurity is the practice of protecting computers, networks, data, and people from digital threats. It matters because schools, hospitals, businesses, governments, and individuals all depend on connected systems. A single weak password, unpatched device, or careless click can expose private information or disrupt important services. Strong cybersecurity combines technology, good habits, and careful risk management.
At its core, cybersecurity tries to preserve confidentiality, integrity, and availability, often called the CIA triad. Defenses such as encryption, authentication, firewalls, backups, and monitoring reduce the chance and impact of attacks. Attackers often use malware, phishing, stolen credentials, or software vulnerabilities to gain access. Effective security uses multiple layers so that one failure does not automatically compromise the whole system.
Key Facts
- CIA triad: confidentiality protects secrecy, integrity protects accuracy, and availability keeps systems usable.
- Risk = likelihood x impact, so high-probability and high-damage threats deserve the most attention.
- Authentication verifies identity, while authorization decides what an authenticated user is allowed to do.
- Encryption converts readable data into ciphertext using a key, so intercepted data is difficult to understand.
- Multi-factor authentication improves security by requiring at least two proof types, such as password plus phone code.
- Backups support recovery after ransomware, deletion, or hardware failure when they are tested and stored separately.
Vocabulary
- Cybersecurity
- Cybersecurity is the set of tools, rules, and practices used to protect digital systems and information from attack or misuse.
- Malware
- Malware is harmful software designed to damage systems, steal data, spy on users, or gain unauthorized control.
- Phishing
- Phishing is a social engineering attack that tricks people into revealing information or clicking a malicious link.
- Firewall
- A firewall is a security system that filters network traffic based on rules about what should be allowed or blocked.
- Encryption
- Encryption is the process of scrambling data so it can only be read by someone with the correct key.
Common Mistakes to Avoid
- Using the same password everywhere, because one leaked account can let attackers try the same login on many other services.
- Ignoring software updates, because updates often fix known vulnerabilities that attackers actively search for.
- Trusting messages just because they look official, because phishing emails can copy logos, names, and writing styles from real organizations.
- Thinking antivirus alone is enough, because cybersecurity also needs backups, strong authentication, safe behavior, monitoring, and access control.
Practice Questions
- 1 A company estimates that a data breach has a likelihood score of 0.20 per year and an impact cost of $500,000. Using Risk = likelihood x impact, what is the expected annual risk cost?
- 2 A password system allows 26 lowercase letters and uses passwords that are exactly 6 characters long. How many possible passwords exist if repetition is allowed?
- 3 A student receives an urgent email claiming their school account will be deleted unless they click a link and log in immediately. Explain at least three signs that could indicate phishing and describe a safer response.