Cybersecurity Basics Cheat Sheet
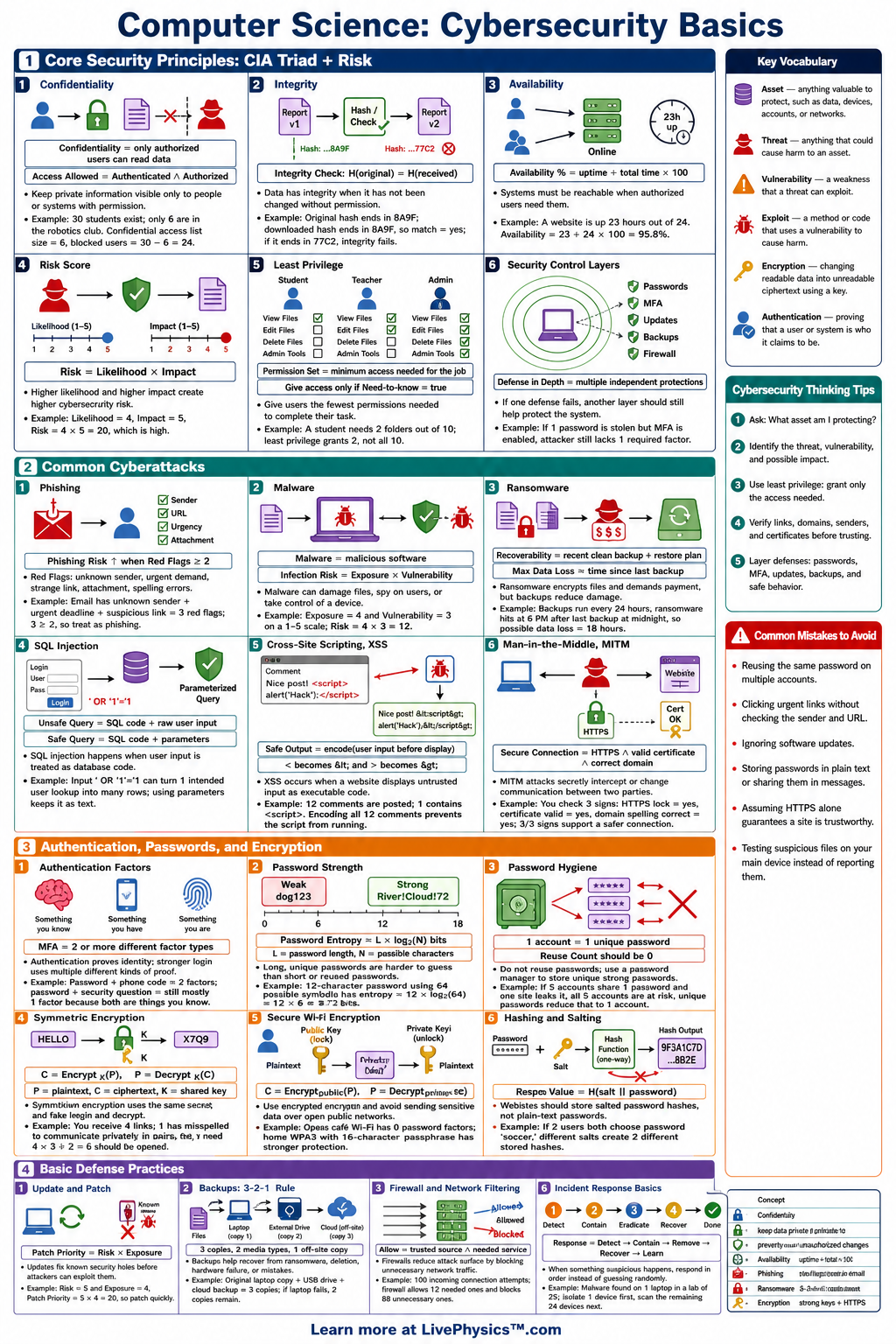
A printable reference covering the CIA triad, authentication, encryption, passwords, phishing, malware, network safety, and risk scoring for grades 8-12.
Related Tools
Related Labs
Related Worksheets
Cybersecurity basics covers how people, devices, networks, and data are protected from attacks, mistakes, and unauthorized access. Students need this cheat sheet to recognize common threats and choose safer actions online. It also connects everyday security habits to core computer science ideas such as data protection, identity, and risk. The most important ideas include the CIA triad, which means confidentiality, integrity, and availability, plus authentication, authorization, encryption, and backups. A useful risk formula is risk = likelihood x impact, where higher likelihood or higher impact means stronger protection is needed. Good security uses layers, such as strong passwords, multi-factor authentication, updates, least privilege, and safe behavior.
Key Facts
- The CIA triad stands for confidentiality, integrity, and availability, and it describes the three main goals of information security.
- Risk can be estimated with the formula risk = likelihood x impact, using consistent scales such as 1 to 5 for each value.
- A strong password should be long, unique, and hard to guess, and password strength increases greatly as length increases.
- Multi-factor authentication improves security because it requires at least two factors, such as something you know, something you have, or something you are.
- Encryption protects data by converting plaintext into ciphertext using an algorithm and a key, so ciphertext = encrypt(plaintext, key).
- Hashing creates a fixed-length fingerprint of data, and a secure password system stores salted hashes instead of plaintext passwords.
- The principle of least privilege means each user or program should have only the access needed to do its job.
- The best response to suspected phishing is to stop, verify the sender through a trusted channel, and avoid clicking links or opening attachments.
Vocabulary
- Confidentiality
- Confidentiality means keeping information private so only authorized people or systems can access it.
- Integrity
- Integrity means keeping data accurate, complete, and unchanged unless an authorized change is made.
- Availability
- Availability means systems and data are accessible to authorized users when they need them.
- Authentication
- Authentication is the process of proving identity, such as by using a password, security token, fingerprint, or login code.
- Encryption
- Encryption is the process of transforming readable data into unreadable ciphertext using a key.
- Malware
- Malware is harmful software designed to damage systems, steal data, spy on users, or gain unauthorized control.
Common Mistakes to Avoid
- Reusing the same password on many sites is unsafe because one data breach can expose several accounts at once.
- Clicking a link in an urgent message without checking the sender is risky because phishing attacks often use fear or time pressure to trick users.
- Thinking antivirus software alone provides complete protection is wrong because attackers can also use social engineering, stolen passwords, and unpatched software.
- Ignoring software updates is dangerous because updates often fix known security vulnerabilities that attackers can exploit.
- Giving every user administrator access is poor security because one compromised account can make wider system damage much easier.
Practice Questions
- 1 A school rates the likelihood of a phishing attack as 4 and the impact as 5 on a 1 to 5 scale. Using risk = likelihood x impact, what is the risk score?
- 2 A password system allows 26 lowercase letters. How many possible 3-character lowercase passwords are there if repetition is allowed?
- 3 A file has a backup made every 24 hours. If the original file is corrupted at 3:00 p.m. and the last backup was at 8:00 a.m., how many hours of work might be lost?
- 4 Explain why multi-factor authentication can still protect an account even if an attacker learns the password.